System Requirements
System Requirements Document (SRD)
1. Introduction
The objective of this project is to design and develop a scalable, AI-powered hybrid (Edge + Cloud) surveillance system capable of:
- Monitoring 1,000+ cameras initially (scalable to 5,000–10,000+).
- Providing real-time intelligent detection.
- Delivering automated voice response (AI agent-based intervention).
- Enabling centralized dashboard-based monitoring.
- Reducing manual security oversight.
- Supporting proactive threat prevention.
This system will leverage a hybrid infrastructure model combining edge computing for real-time responsiveness and cloud computing for advanced analytics and scalability. AWS has been selected as the cloud provider to ensure robust scalability, security, and compliance with industry standards such as GDPR and SOC 2.
2. System Overview
2.1 Hybrid Infrastructure Model
The system will utilize a hybrid infrastructure model, as discussed in the meeting AI-Surveillance-System-Discussion, comprising:
Edge Layer (On-site – Jetson or equivalent GPU devices):
- Real-time object detection.
- Motion tracking.
- Zone monitoring.
- Immediate voice response trigger.
Cloud Layer (AWS Cloud Services):
- Advanced analytics.
- LLM-based contextual reasoning.
- Event classification.
- Centralized dashboard.
- Alert management.
- Data storage & historical analysis.
This architecture ensures:
- Fast response at the edge.
- Scalability and advanced intelligence via the cloud.
- Optimized infrastructure cost-performance balance.
2.2 Compliance and Security
The system will adhere to the following compliance and security standards:
- GDPR: Ensuring data privacy and protection for all collected video and event data.
- SOC 2: Implementing robust security, availability, and confidentiality controls.
- AWS services such as IAM (Identity and Access Management), KMS (Key Management Service), and CloudTrail will be utilized to meet these compliance requirements.
3. Functional Requirements as Story Points
- As an Admin, I should be able to onboard and provision devices remotely.
- As an Admin, I should be able to monitor the health of all devices in real-time.
- As an Admin, I should be able to group cameras by site for easier management.
- As a Security Operator, I should be able to view live camera feeds and event timelines on a centralized dashboard.
- As a Security Operator, I should be able to receive real-time alerts for trespassing, unauthorized entry, and loitering.
- As a Security Operator, I should be able to search and filter alerts by type, time, and location.
- As a Security Operator, I should be able to playback historical events for analysis.
- As a Security Operator, I should be able to receive automated voice responses triggered by specific events.
- As an Admin, I should be able to define custom rules for event detection and response.
- As an Admin, I should be able to manage user roles and permissions for the system.
- As an Admin, I should be able to configure client-specific encryption keys for sensitive data storage.
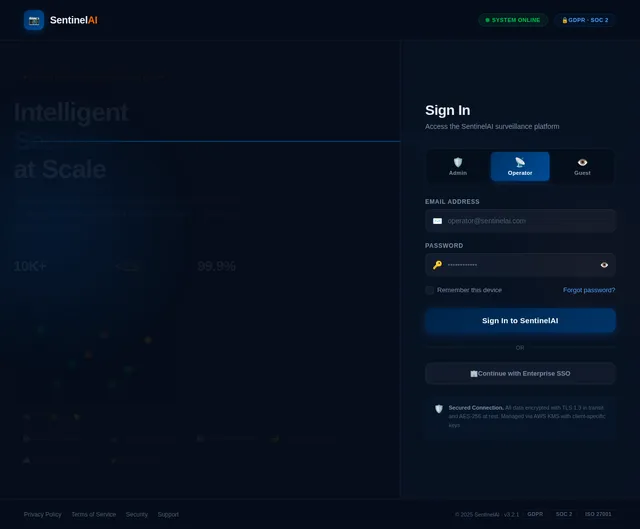
4. User Personas
4.1 Admin
- Responsible for system setup, device provisioning, and user management.
- Oversees compliance and security configurations.
- Defines custom rules for event detection and response.
- Configures client-specific encryption keys for data security.
4.2 Security Operator
- Monitors live feeds and event timelines.
- Responds to real-time alerts and notifications.
- Analyzes historical data for incident reporting.
4.3 Guest (Optional Future Persona)
- Limited access to specific camera feeds or event data (e.g., for external auditors or stakeholders).
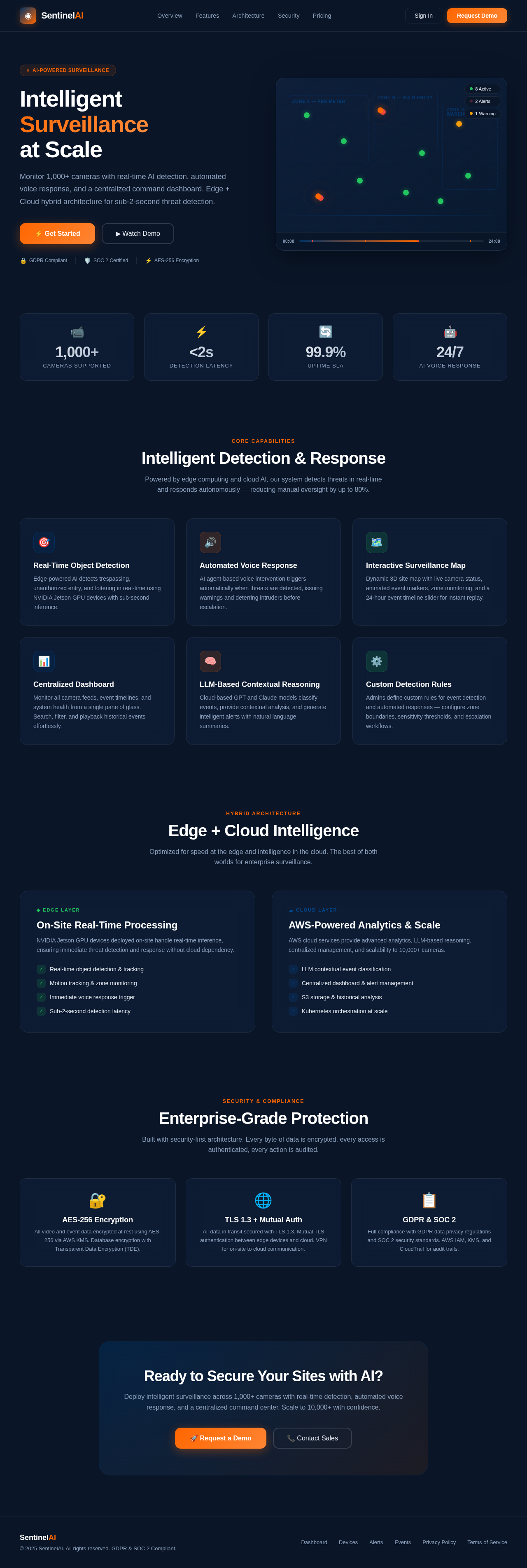
5. Visuals Colors and Theme
Proposed Color Theme:
- Primary Colors: White (#FFFFFF) for a clean, modern, and professional look.
- Accent Colors: Deep Blue (#003366) for key elements and Bright Orange (#FF6600) for alerts and notifications.
- Background Colors: Light Gray (#F2F2F2) for subtle contrast and section separation.
- Typography: Clean and modern sans-serif fonts like Roboto or Open Sans.
Theme Concept:
The design will emphasize clarity and usability with a focus on a bright, white-themed interface. The dashboard will use color-coded indicators (e.g., red for critical alerts, green for healthy devices) to enhance user experience. The white theme will create a sense of openness and simplicity, ensuring that users can focus on critical information without distractions.
6. Signature Design Concept
Interactive Surveillance Map with Dynamic Event Visualization
The homepage will feature an interactive 3D map of the monitored site(s), showcasing camera locations and real-time event activity. Users will see:
- Dynamic Camera Icons: Each camera will be represented by an icon that changes color based on its status (e.g., green for active, red for alert).
- Event Animations: Real-time events (e.g., trespassing, loitering) will appear as animated markers on the map, with contextual pop-ups providing details.
- Zoom and Pan: Users can zoom in to specific zones or pan across the site for a detailed view.
- Event Timeline Slider: A timeline slider at the bottom of the map allows users to replay events from the past 24 hours, with markers appearing on the map as they occurred.
The map will be visually stunning, with smooth transitions, hover effects, and a dark mode option for night-time monitoring. This feature will make the system instantly engaging and provide a competitive edge over traditional surveillance dashboards.
7. Non-Functional Requirements
- Scalability: The system must support 1,000 cameras initially, with the ability to scale to 10,000+ cameras.
- Performance: Real-time detection and alert generation with a latency of less than 2 seconds.
- Security: Data must be encrypted in transit (TLS 1.3) and at rest (AES-256).
- Compliance: Adherence to GDPR and SOC 2 standards.
- Availability: 99.9% uptime for the cloud-based dashboard and services.
- Usability: The dashboard must be intuitive and require minimal training for operators.
8. Tech Stack
Frontend
- React for Web.
Backend
- Python.
- FastAPI.
Database
- MySQL for structured data.
- Alembic for database migrations.
AI Models
- GPT 5.2 for user-friendly responses.
- Claude 4.5 Opas for coding and academic tasks.
AI Tools
- Litellm for LLM routing.
- Langchain for AI workflow orchestration.
Local Orchestration
- Docker.
- Docker Compose.
Server-Side Orchestration
- Kubernetes.
Cloud Provider
- AWS (Amazon Web Services):
- S3 for storage.
- Lambda for serverless processing.
- IAM for access control.
- KMS for encryption (including client-specific keys).
- CloudTrail for compliance monitoring.
9. Assumptions and Constraints
- The system will initially be deployed in regions where AWS services are available.
- Data retention policies will be defined during the implementation phase.
- The edge devices (e.g., NVIDIA Jetson) must be compatible with the system's AI models.
- The system must comply with GDPR and SOC 2 standards.
- Client-specific encryption keys will be configured for sensitive data storage.
10. Encryption Methods for Stored and In-Transit Data
Data Encryption at Rest
- AES-256 Encryption: All video and event data stored in AWS S3 will be encrypted using AES-256.
- AWS KMS (Key Management Service): Encryption keys will be managed using AWS KMS, ensuring secure key storage and rotation.
- Client-Specific Keys: Each client will have dedicated encryption keys managed through AWS KMS, ensuring data isolation and security.
- Database Encryption: MySQL databases will use Transparent Data Encryption (TDE) to encrypt data at rest.
Data Encryption in Transit
- TLS 1.3: All data transmitted between edge devices, cloud servers, and the dashboard will be encrypted using TLS 1.3 for secure communication.
- Mutual TLS Authentication: Edge devices and cloud services will authenticate each other using mutual TLS to prevent unauthorized access.
- VPN: A Virtual Private Network (VPN) will be used for secure communication between on-site edge devices and cloud infrastructure.
11. Glossary
- Edge Layer: On-site hardware for real-time processing.
- Cloud Layer: Remote servers for advanced analytics and storage.
- GDPR: General Data Protection Regulation, a European Union law on data protection.
- SOC 2: Service Organization Control 2, a standard for managing customer data.
- LLM: Large Language Model, an AI model for natural language processing.
- IAM: Identity and Access Management, a framework for managing user permissions.
- KMS: Key Management Service, a tool for encrypting and managing cryptographic keys.
- TLS: Transport Layer Security, a protocol for encrypting data in transit.
- AES-256: Advanced Encryption Standard with a 256-bit key, used for encrypting data at rest.
This updated SRD now reflects the requested white theme for visuals and maintains all other critical details. Let me know if further adjustments are needed!

No comments yet. Be the first!